I'll get calls from people whose computer has been compromised after they opened an email and or clicked on a link it contained. They don't understand why their anti-virus software didn't protect them.
Let's have a look at a potentially nasty email spoof (bogus, fake email) a client received just this morning. No worries - it's safe in the form I'm presenting it here since these are just screen captures.
Here's the email showing a relatively innocuous link at the bottom and a "trusted source" at the top - apparently from a department in Staples:
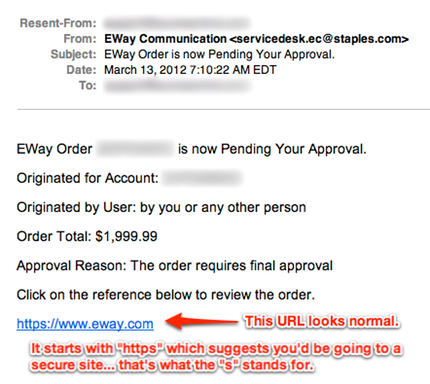
This is what we learn when we hover - DON'T CLICK - over the link:

When the URL you WOULD go to is researched (the one in the yellow tool tip), we find it's associated with a number of phishing scams. As defined by Wikipedia, Phishing is:
a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT administrators are commonly used to lure the unsuspecting public. Phishing is typically carried out by e-mail spoofing or instant messaging, and it often directs users to enter details at a fake website whose look and feel are almost identical to the legitimate one.
How did this get past the anti-virus software? There are two types of email spoofs: active and passive. The example above is of a passive email spoof.
Active Email Spoofs: The active email spoofs contain an attachment - a file, photo, song, video, etc. These are particularly bad because as soon as the email is opened, its payload (the attachment) is deployed (activated). Sidebar: this is why having your email preview pane option on is dangerous - you have no chance to think about a suspicious email before your software auto-opens it. In those first few seconds, unless your anti-virus software is up todate and able to detect that email spoof's particular payload, your computer will be compromised. Period.
What to do? Pull the plug!
- IMMEDIATELY unplug your computer's wired connection to the internet. Literally, unplug the ethernet cable that delivers the internet to your computer.
- If your computer uses a wireless connection to the internet, disable it. Know where the hard button is on the outside of your notebook and use that since the infection may render your ability to turn off the wireless capability using your mouse impossible.
- Get your anti-virus scanning your entire computer - NOW, not 2, 15, 30 or more minutes later... NOW!
- Contact your I.T. support person/people of choice and make them aware that you may need them.
Time is of the essence in computer infections/hijacks/compromises! The faster you get your computer's defence systems on the offensive, the better your chances of containing the potential infection. The longer a compromised computer has access to the internet the more likely it is that your personal information can be stolen, the more likely it is that secondary, tertiary and more infections can take place to the point where the system is so badly compromised that the computer is beyond saving.
Passive Email Spoofs: Like our example, above, have nothing actively malicious in them. Instead, they wait until the user clicks their link(s) to take the user to a website that isn't the intended destination. Upon the user's browser arriving at the malicious site, depending upon the browser settings, any number of components may be downloaded through the browser which hijack it or infect the computer. In this case the anti-virus may not kick in because the components downloaded were allowed by virtue of the browser settings... Active-X components, Flash media, etc. the elements that our browsers need to provide a full experience to the websites we visit. Sadly, among the first components that can infect computers this way are ones that redirect browsers to the same or other infected websites only to download even more malware, knock out anti-virus software, change the administrator account password, and the list goes on. Again, having an updated anti-virus program is a good defence, but being aware of the links you are clicking is really the first line of defence.
What to do? The same steps as detailed above for the active email spoofs.
So, let's review:
- if you receive an email from someone you don't recognize, DON'T OPEN IT, instead delete it.
- if you open an email and it's asking you to click a link... READ the email... did you order the product or service it's about? If not, delete it.
- if an email is asking you to click a link... hover over - DON'T CLICK - the click and check the URL in the yellow tool tip against what is displayed. If they aren't the same or at least look like they're going to take you to the intended website... you guessed it, delete it.
- governments, banks, cell phone companies, and pretty much EVERYONE doesn't use email to verify personal/private/confidential information because email is largely UNENCRYPTED and NOT SECURE. If you get an email asking ANYTHING to do with personal/private/confidential information, delete it.
BEFORE you get hacked, check out:
- the RCMP's website on scams at: http://www.rcmp-grc.gc.ca/scams-fraudes/index-eng.htm
- the Canadian Anti-Fraud Centre at: http://www.antifraudcentre-centreantifraude.ca/index-eng.htm
AFTER you get hacked or you think you've been a victim of identity theft or fraud, use the RCMP Identity Theft and Identity Fraud Victim Assistance Guide or download it as a PDF. Remain calm and work through the steps.
If you are feeling like firing one back on the bad guys, forward the offending email to the organization that the email purported to be from. Most organizations have an email address specifically for reporting email abuse/scams.
Until next time!
Bob